How to Find the Memory Address of a Symbol in an ELF File
A quick and useful tip for locating symbol memory addresses in ELF files using arm-none-eabi-nm combined with grep—perfect for embedded debugging scenarios like setting up SEGGER RTT or inspecting linker placements and runtime symbols.
Here’s a handy tip that came up during some work with SEGGER RTT (Real Time Transfer).
When initializing an RTT session, you need to provide the memory address of the RTT static control block variable. While it’s possible to dig through your generated .map file, there's a faster way:
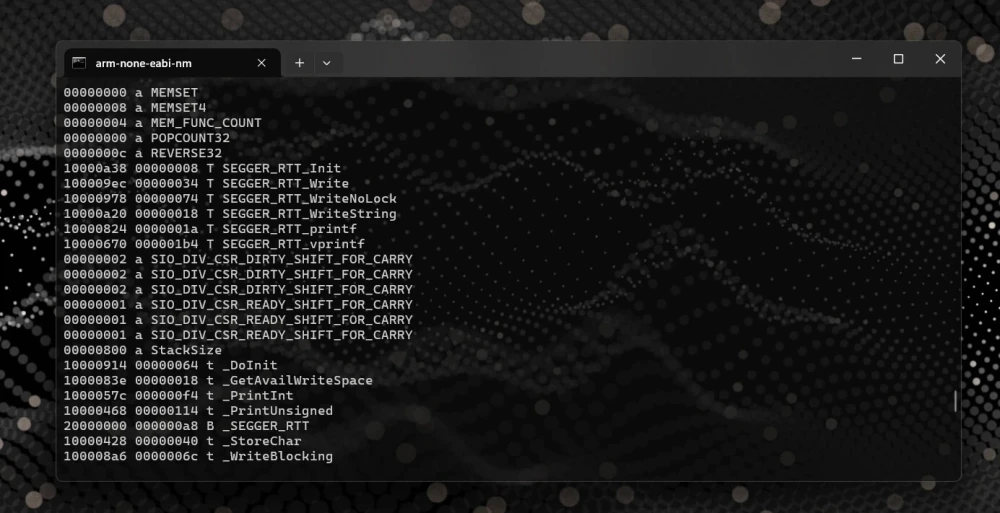
arm-none-eabi-nm blink.elf | grep _SEGGER_RTT
20000000 B _SEGGER_RTTBy piping the output of arm-none-eabi-nm (which lists all symbols in your .elf file) to grep, you can quickly isolate and retrieve the memory address of your desired symbol.
Note: For Windows users, grep is typically a Linux command. However, you can easily use this trick with tools like WSL (Windows Subsystem for Linux), Cmder, or Git Bash.
arm-none-eabi-nm firmware.elf | grep foo
1000033c T fooThis technique isn't limited to variable addresses, it's equally useful for finding function or constant data addresses. Variable symbols are typically stored in volatile RAM, while function code and constant data usually reside in non-volatile ROM or Flash memory, reflecting their runtime mutability or immutability.

How to Embed Binary Information in Your Rust Pi Pico Firmware
Embed binary metadata in your Rust Pi Pico firmware with picotool! Learn how to store program names, versions, build dates, and more in flash, so you can easily track firmware details with a single command.

Welcome to The Crab Lab: Diving into Embedded Rust (and Maybe Some Memes)
Are ya ready, Kids? Dive into The Crab Lab, a new series exploring Embedded Rust through tutorials, projects, and troubleshooting tips. Join the journey of learning, experimenting, and building with Rust on microcontrollers.
Cortex-M0 Profiling: How to Trace Without Hardware Support
The ARM Cortex-M0 and M0+ lack hardware tracing features like SWO, ETM, and ITM, so how do you profile code on them? In this post, I explore software-based techniques to get deeper insight into performance and debugging on these resource-constrained MCUs.
Whether you're building something new, fixing stability issues, or automating what slows your team down — we can help.

